People Recon With Recon-ng. An easy cheat sheet.
This practical Recon-ng tutorial covers social modules. Learn to easily perform reconnaissance on your target.
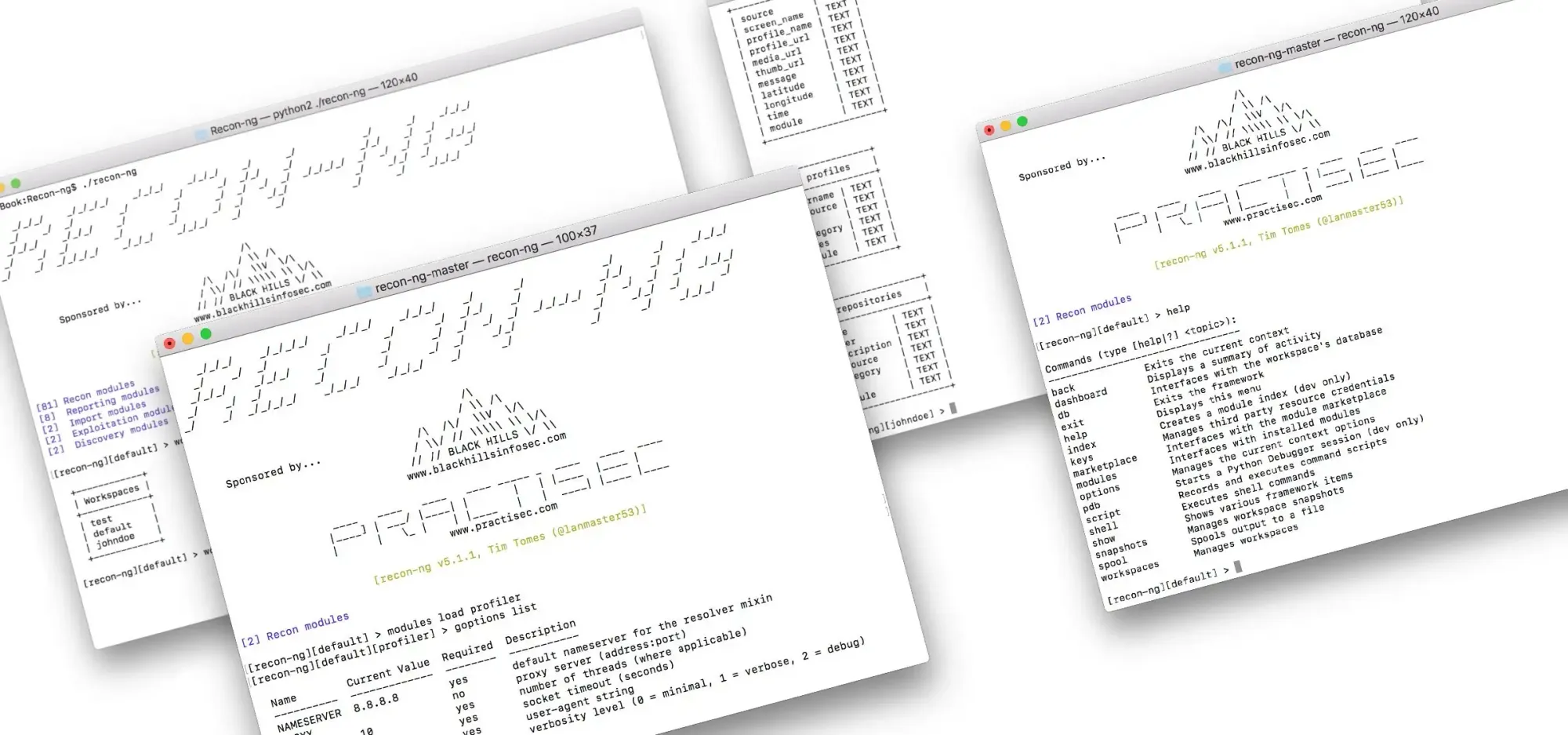
Recon-ng is an excellent tool for information gathering in the early stages of penetration testing. It was briefly mentioned in my previous OSINT article, and this one will cover the tool more in detail. Recon-ng comes with people reconnaissance modules, which will be described in the article.
Workspace setup
Workspaces keep related information in a single container and prevent mixing of different projects. They also help to store information after you exit the tool, so the work can be continued later. Recon-ng starts with the default workspace. Use the following commands to manage workspaces.
workspaces add workspace_name

Modules
Import
The Import/list module saves a lot of time when there are multiple data entries. Rather than manually entering information, it can be done by importing data from the list.
To successfully import data into tables their schema has to be followed.
Set the variables accordingly to the schema.
set COLUMN username
set FILENAME file_name.txt

Profiler
The Profiler module performs a username search on various websites using WhatsMyName. Usernames are loaded from the “profiles” table. As the import module was previously used, the “profiles” table is already filled with usernames. It can be checked using the following command.
If the table looks good — select the module and run it.
The Twitter_mentions module leverages the Twitter API to enumerate users that were mentioned by the given handle. Twitter_mentioned moduleenumerates users that mentioned the given handle. After enumeration is completed the “profiles” table updates with the results. Note, that Twitter module requires an API key and limits searchable tweet history to 7 days. If you need more history, then use the Twitter machine in Maltego, it doesn’t have history limits. If using Twitter profile for Maltego integration or applying for a developer account looks troublesome — get Twint, it works without API key and integrations.
When the module is selected — set the Twitter username and run it.

Have I been pwned
The Hibp_breach module leverages the haveibeenpwned.com API to determine if email addresses are associated with breached credentials. After the scan is done the “credentials” tableis filled with the compromised emails.
If the is no data in the “contacts” table — add it and run the module.
After the scan is done — check the “credentials” table for results.

Whois POC Harvester
The Whois_pocs module uses the ARIN Whois RWS to harvest POC data from whois queries for the given domain. After the scan is done the “contacts”table updates with the results.
When the module is selected — set the source and run it.