I need to find someone online. Where to start?
Learn faster and more effective ways to search

What is the reason for finding the true identity of someone on the Internet? There are many of them. In the worst-case scenario, you could be a victim of online fraud or a hack. In both cases, the bad guy has taken steps to make sure his true identity is cloaked. The article will cover search techniques that will be useful not only in such extreme scenarios but also to find a perfect candidate for the job or perform competitive intelligence and penetration testing.
There are many paths you can take to find information. Some of them are shorter than others, so choosing the right one at the very beginning might save you a lot of time. It depends on what information you have to begin with, but with certain starting data points you will obtain more reliable information faster.
Where to start?
Your first step is to analyze the problem. What exactly do you want to find out? A user’s real name? A physical address? A phone number?
Search engines
Generally, an investigation starts with a broad search, typically using a search engine. These search results can then be refined to eliminate false positives — other people with the same name. If your target has a common name you may get billions of hits in a search. With practice, you can craft a search that focuses on things you know about your target. You should make two lists: what you know and what you don’t (but need) to know.
As was said before, a search engine is usually the first place you go searching for the information. Use items from the list of things you know as search terms. On the other hand, if you have the social media profile or any other direct link that you have confirmed 100% belongs to the target, then it’s better to start from the social media first and then proceed to search engines with the information you collected.

The more specific information you have — the more focused your queries should get. For example, let’s research the scam account above. Looking at it we can compose a focused query, searching for other accounts that mention its handle on Twitter.
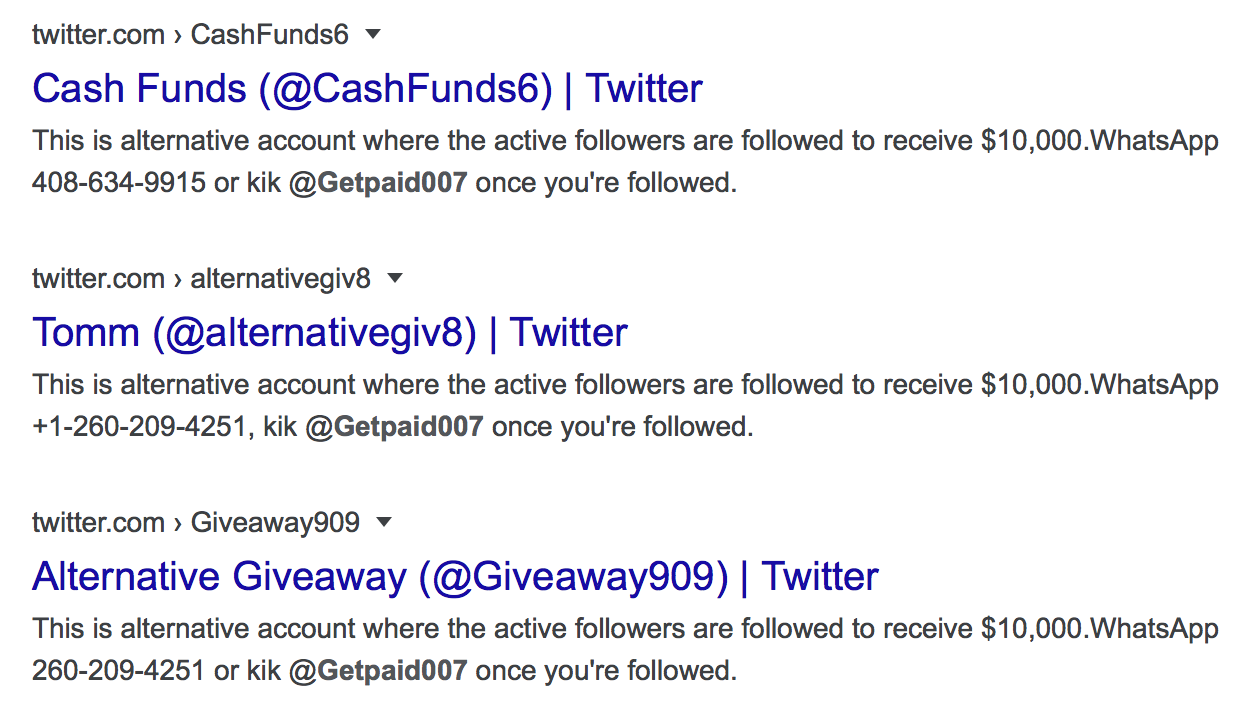
The quoted search gave us more relevant results that we can further refine.
Unique identifiers
The unique identifier is the data point that belongs only to one person. For example, there are no two identical emails that belong to different people. However, Googling a username or a name you might get results that belong to multiple people. Paul Myers concisely summed up the importance of the email:
An email address is unique (a name isn’t). It often incorporates a name. Sometimes it incorporates user name. It reveals a country. Sometimes an employers name or domain name. It can be used in a people search to discover a phone number.
[#OSINT] When collecting information on a person, what’s usually the most valuable piece of information you can have or find?
— Jake Creps (@jakecreps) December 28, 2019
The phone number can be considered as a unique identifier, but in some countries the phone number is transferred to another person if not used for a while. Phone number reveals the country more accurately than the email. For example, you can use Google Mail in any country but having a phone number of other countries is problematic for local use.
The process
It’s important how you organize and structure the information. Mindmaps help you to do the job and see the whole picture. The one provided by WebBreacher (XMind file) is pretty extensive.
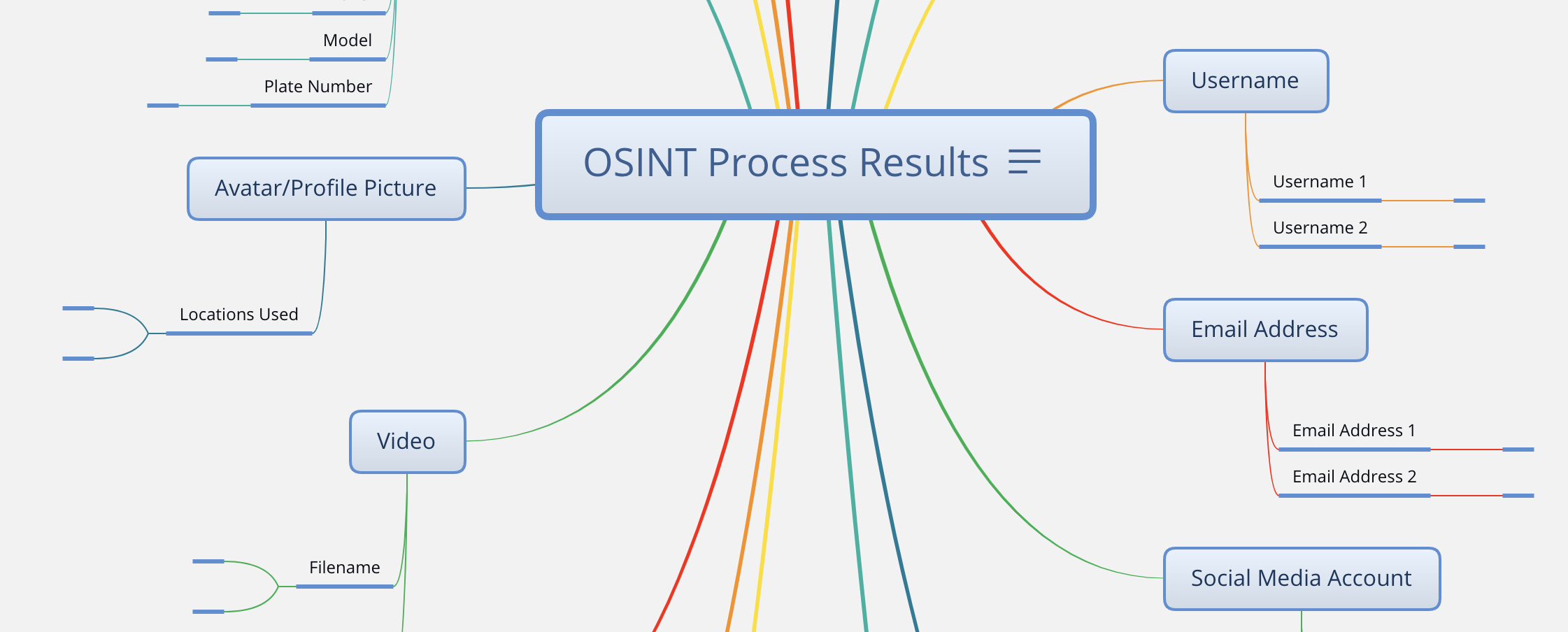
The whole research process is based on assumptions and going down the rabbit hole to prove them. The more information you have, especially the structured one — the easier it will be to make assumptions. Some of them will lead you to dead ends, so don’t give up.
Web search
As was mentioned above, it’s better to start from the quoted search, rather than from the general search queries. It will help you to narrow down the search and get more relevant results from the beginning. A web search might lead you to public records that contain more truthful information than social media. Learn and use some of the advanced search features that most search engines have built in.
Username
To find social accounts with the researched username you can use online services like Namechk or Checkusernames. These are good when you want to have a simple experience and don’t have a lot of usernames to check.
The second option is the Terminal tools. Running scripts locally instead of using websites will give you more flexibility, like searching for several usernames at once, load data from a JSON (file format, that stores information in an organized, easy-to-access manner), use proxies (gateway between you and the internet), etc.
Username search might be tricky on websites that use IDs along with usernames. For example, Vkontakte users might not always have a username unless they create it.
As was said before, email is a unique identifier and a preferable starting point. If you don’t have the target’s email — try to find it using Hunter. Having an email address that produces no search results should raise you the question: “Is this email valid?”. Use validation tools, like Verifalia to test the email. Also, when the email you are researching does not appear in any breach — it might be a “burner” or just recently created. Getting positive results in Haveibeenpwned or any other breach checker tells not only the services it was used to sign up for but the email’s age as well.
Don’t limit yourself to the emails you have, assume your target has other ones, so try to compose a list and validate your assumptions. Proofy can help to validate the created list by uploading a .txt or .csv file. Melissa is another good source. Generating assumptions manually can be challenging, but an Email permutator will simplify the process.
Another useful technique is to type your target’s email on the websites and see the response. For example, use email on apple ID to create an account and see if the profile with the following email exists.
Phone number
The first thing you should do with the phone number is to add it to your phones’ address book and check it on messengers.
Secondly, check the number against reverse caller ID apps. Remember, that these services harvest your contacts for its database when you sign up. Therefore, it’s better to sign up with a fake email or by an app on a burner phone. TrueCaller and GetContact can be a goldmine of information, as sometimes people instead of surname write home address, occupation, or any other sensitive information, that may be useful when researching your target.
Thirdly, check the phone number against online banking services. Online banking accounts have a true name and surname, as opposed to social networks, where people might use aliases.
Image
Firstly, check the image for metadata using online services (exifdata.com and viewexifdata.com) or use locally installed tools (Exiftool and FOCA). Obtaining GPS location or other EXIF data at first is a good starting point during image analysis and demands less effort than the next two steps. Be aware that Facebook and other social media sites strip out the EXIF data.
Secondly, do the reverse image search — it might help to find pages that you wouldn’t have stumbled upon using text queries. The better resolution of the uploaded image — the more precise results you will get. Don’t just perform a reverse image search on the avatar but on the cover image as well, if the profile has one (like on Facebook or LinkedIn). Also, if the image is not sharp — you can deblur it to get better results.
Somdev Sangwan did a good job explaining it in “Deblurring images for OSINT”. Here are the most popular reverse image search services:
- Yandex — has good facial recognition algorithms, which makes it the first image search tool to use in the persona investigation.
- Google — the most popular reverse image search engine, but not as good as Yandex at identifying people.
- Bing — allows to crop a picture and search within the image, which helps to narrow down the search.
- Baidu — good for content that originates from China, and does not perform well on Europe-focused searches.
- FindClone — works very well and searches only for Vkontakte users. It’s a to-go tool for VK-focused investigations.
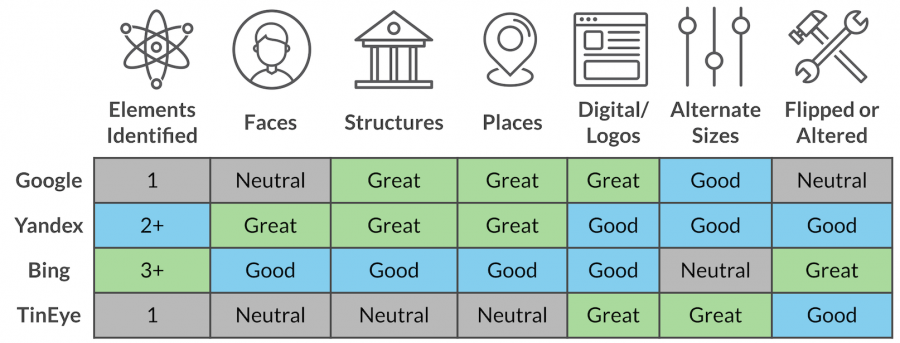
Here are a couple of articles that do a deep comparison of search engines and tell which one is the best depending on the specific use case.
- Guide To Using Reverse Image Search For Investigations by Bellingcat
- A Brief Comparison of Reverse Image Searching Platforms by Craig Silverman
- How to Find Out Someone’s Name From a Picture by Jan Tegze
Thirdly, use GEOINT techniques (analysis of images and data associated with a particular location) to get the location if it’s still not known after the first two steps were performed. The “Finding McAfee” article by Benjamin Strick shows some useful methods.
Writing style
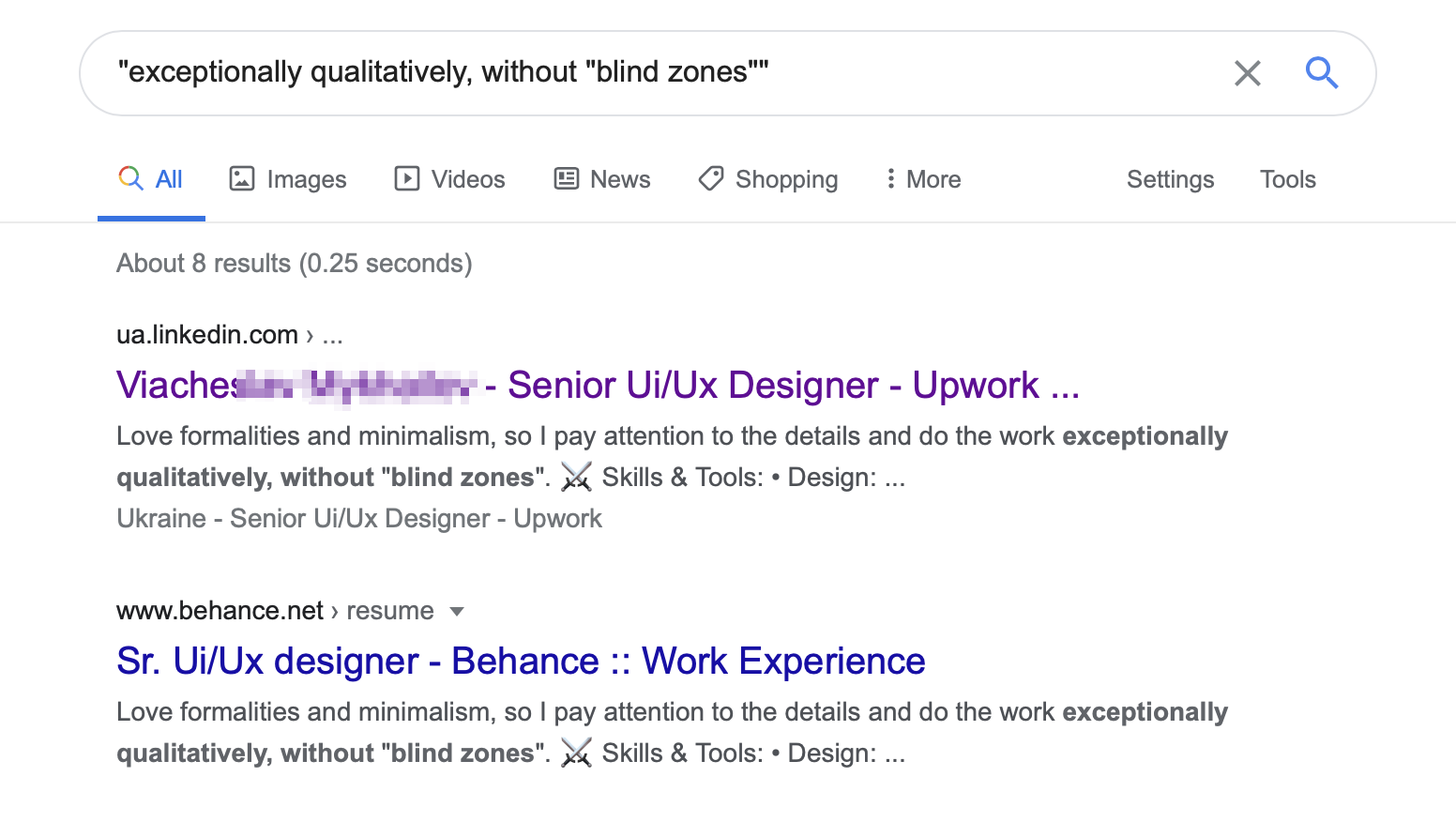
Some people have a distinguishable writing style and use unique word combinations. Doing a quoted search on specific words or symbol combinations they use might give you new leads. For example, as a recruiter, you might look for candidates on anonymous job search websites.
Reading the vacancy above the highlighted phrase stands out. If used elsewhere, was assumed, it will give several focused results and it did. Thus, real name, picture, and other identifying information was obtained.
Now when you know where to start it is time to learn more generic search techniques. The article below covers the topic more broadly.


